A continuous process to improve security posture
Vulnerability Management Service
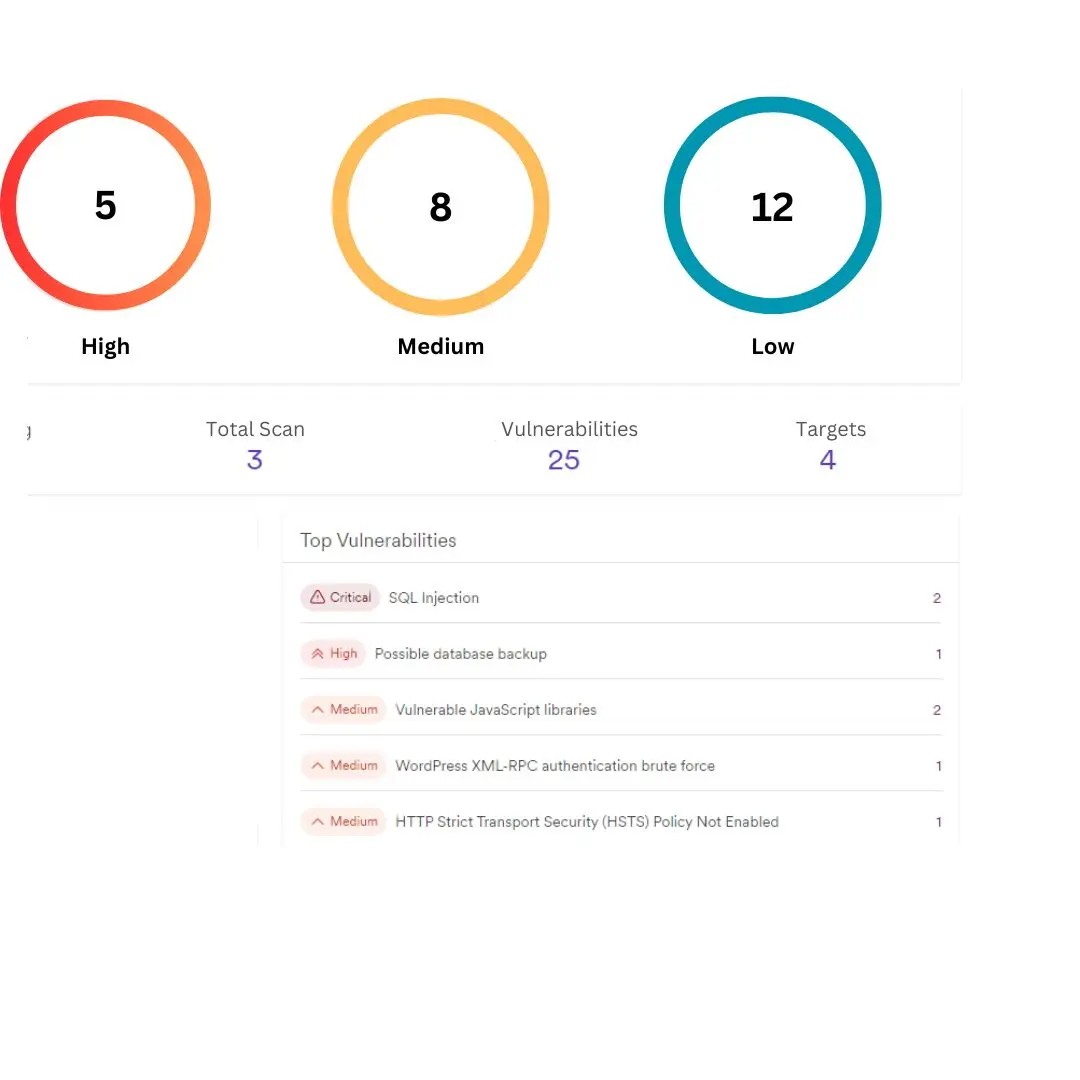
Vulnerability management is an ongoing process of identifying, prioritizing, and remediating vulnerabilities in digital systems. We utilize our skills and various vulnerability management tools to scan your systems regularly, report to you, and help you remediate before it is too late.
Get started TodayToday’s Clean Scan Doesn’t Guarantee Tomorrow’s Security
Security is dynamic, with new threats emerging constantly. Continuous vulnerability management is crucial for defending against evolving threats. Our services stay ahead of challenges to keep your systems secure over time.
Every Month
Scheduled Scan
All your networks, applications, and systems are scanned for vulnerabilities on a schedule and on-demand, combining manual and automatic scanning.
Unbeatable
Perfect Result
Professionals assess and prioritize risks, providing ongoing support for remediation and patching. Additionally, a detailed report is furnished.
Tools
Top Tools
We use the award-wining commercial, custom, and open-source tools that reduce the costs but still produce unbelievable result.
Often under attack? Explore our vulnerability management service and stay safe!
Continuous Security Improvement
Our Vulnerability Management Lifecycle
Are you under frequent attack?

Why Vulnerability Management?
Vulnerability management is an ongoing process if you want to monitor security continuously and improve the security posture over time.
Purpose and Frequency
Vulnerability assessment is a one-time assessment, whereas vulnerability management is an ongoing process of monitoring and identifying vulnerabilities and supporting remediation and mitigating them.
Scope
Vulnerability assessment usually a method to detect and classify vulnerabilities but vulnerabilities management is broader such as risk assessment, prioritization, and implement of other strategies to address them.
Outcome and Value
Vulnerability assessment result detail report of founded vulnerabilities and their impact, and vulnerability management is a strategic approach to enhance overall security by monitoring security continuously.
Key Benefits
Why Choose Us
Expertise and Experience
Our team is holding different type of prestigious cert including OSCE3, OSEP, OSWE, OSCP and brings a wealth of knowledge and experience in vulnerability management.
24/7 Support
Day or night, create tickets and call or email us for instant support whenever you need it. We are dedicated to your satisfaction.
Tailored Solutions
Bytium customizes the vulnerability management services to your requirements, which helps to reduce costs and increase productivity.
One-stop Security Shop
We are a cybersecurity-managed IT Services provider ready to provide you with essential to advanced IT support globally, including the USA, UK, Bangladesh, and
Enhance Security With Real-Time Monitoring
Optionally stay one step ahead with our real-time security monitoring with our managed open-source SIEM.
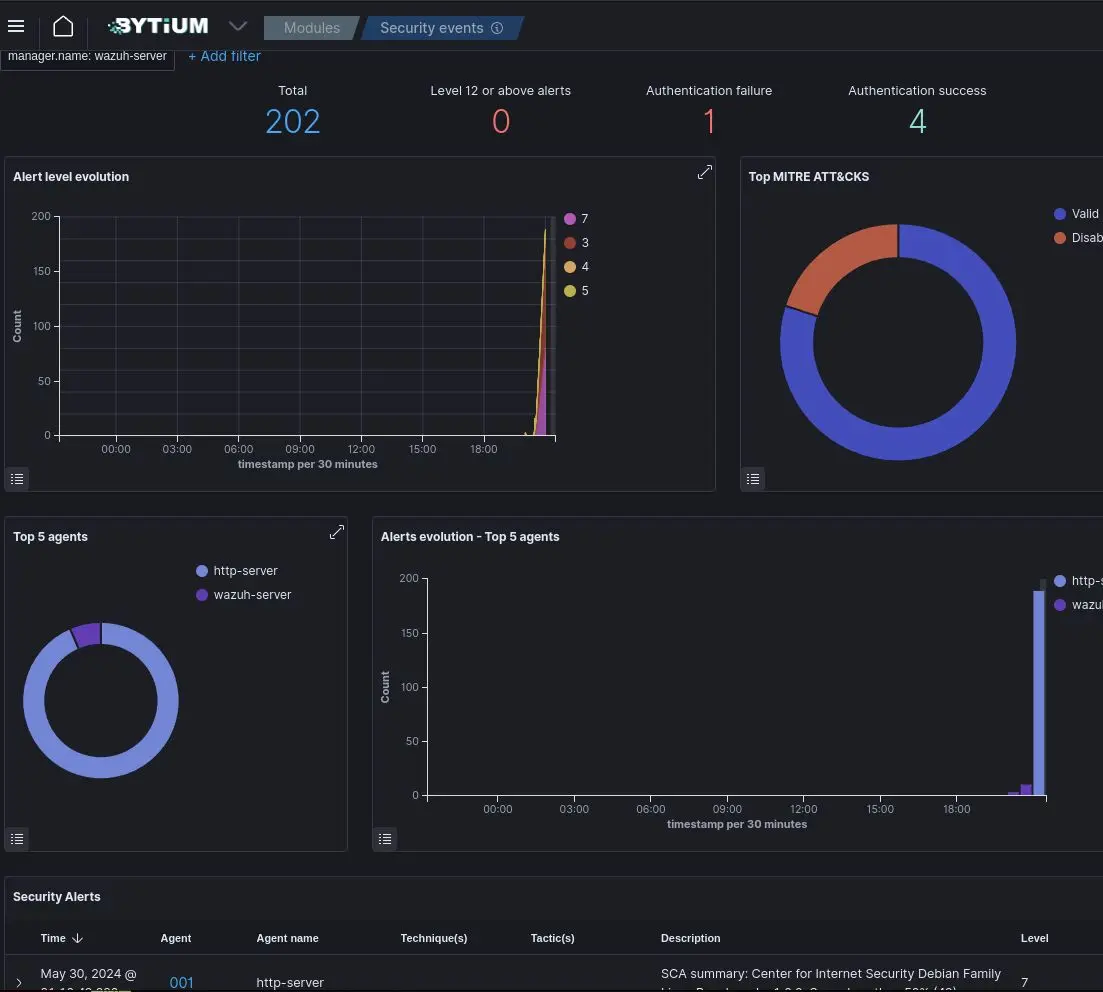
Proactive Vulnerability Management
By leveraging advanced trend and pattern analysis, SIEM can forecast potential future threats and vulnerabilities. This empowers organizations to take proactive measures to address risks before they escalate into actual threats.
Real-time Threat Detection
Monitor network traffics and detect anomalies and potential threats in real-time. Security incident occurred, someone attacking your systems? Block them instantly.
Centralized Security Management
SIEM collect and analyze data from various sources which is valuable for forensics, reducing false positive, and taking action against new attack types.
Do you want to utilize a SIEM with Vulnerability Management?

FAQ
Vulnerability management is ongoing process of identifying vulnerabilities and improving the security posture overtime.
This is a continuous process, not a one-time assessment. If vulnerabilities do not exist today, there is no guarantee they won’t arise tomorrow. Most vendors engage with MSP on a yearly basis. And if the MSSPs have the ability, they will perform the vulnerability scanning at least once or twice every month.
Our company is located in the USA, and our office is located in the UK and Bangladesh, providing service globally.
Yes, we provide customizable service options to fit the unique needs and security requirements of your organization. Services can be tailored during the initial setup and adjusted as needed.
To get started, sign up or contact us through our contact form.
Contact Us
We provide vulnerability management globally including the USA, the UK, and Bangladesh.
Fast Response
Whenever it is cybersecurity talk, we never delay more than 3 hours. Get faster response and faster solutions.
Affordable
You don’t need to break your bank to access our high quality vulnerability management services. Designed to affordable for anyone.
100% Satisfaction
We are dedicated to your 100% satisfaction. If you are unsatisfied with our services, you could ask for a refund! What else do you need?