Bytium, a complete IT solutions company, also provides a comprehensive security review of web applications; recently reviewed the security for a popular Client Relationship Management System made with PHP.
Security Reviewed by: Bytium Cybersecurity team
Application Name: [Hidden for Privacy Reason]
Time Spent: 6 Hours
Context
The CRM application was designed to handle various sensitive tasks like creating estimation, storing customer information, generating invoices, making payments, and other perform other sensitive functionalities. Bytium Team performed a quick security assessment to discover security vulnerabilities in the code with two methods 1. Partial Black box, 2. Code review.
How was our testing approach?
As a team leader, Jobyer engaged with the application’s developer. The application was installed in the local host. Some dummy data was inserted to simulate the application’s usage. We have used the following tools to speed up the process.
- Burp Suite Professional: This was mainly used to perform semi-auto testing.
Note: Most of the assessment was manually reviewing the application’s source code where user input was accepted.
Our Findings!
We have manually reviewed the application structure and source code for the part of the application where user input was accepted. Found followings:
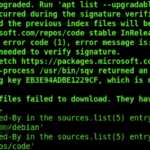
- Server-side errors
- XSS
- HTML Injection
- Server-side request forgery
- Session Issues
- Missing user-input sanitization
Possible Impact
XSS can be used to execute a malicious script in the user’s browser, whereas attacker can use HTML injection for similar attack like phishing by injecting HTML into a existing page.
Cybercriminals can utilize server-side request forgery for data exfiltration, internal network mapping, or even remote code execution.
As some input point was not sanitized, there was the possibility of being a victim of another type of injection attack. Session issues could have been used to steal the user’s session.
Resolution
Bytium team promptly contacted the application’s development team with the following recommendations:
- Details of the discovered vulnerabilities
- Ways to Sanitize Inputs
- Regular vulnerability assessment as part of the development lifecycle.
Conclusion
Bytium found high-risk vulnerabilities that could affect data security. Their manual scanning approach showed the importance of regular security assessments. Improving the app’s security will help protect its users.