The root cause of data breaches is often traced back to not identifying security vulnerabilities at the right time and not remediating them before hackers take advantage. The security hole often goes unnoticed until a hacker breaks in and breaches the sensitive data. Once a data breach occurs, organizations are left to pick up the pieces by fixing issues and regaining customers’ trust, which is generally challenging and expensive. In this article, We will discuss 5 strategies for managing data breaches.
Confirm the Breach
The first step is to confirm whether data breaches are actual or just system malfunctions. Systematically, ensuring data breaches will help you to avoid any unnecessary panic. Find the answer to the following questions as initial signs of data breaches:
- Is there any security alert from your security software like IDS? Or
- Have you been informed by an external security researcher or customers?
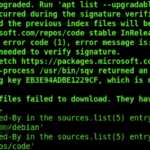
If the answer is positive, immediately involve your IT Security team in gathering as much information about the data breach as possible. Analyze the server logs, any unusual login attempts, and security systems and look for other unexpected activities like large data transfers.
Stop Breach from Spreading
You must take immediate action to prevent the breach from spreading further. This is critical in protecting your additional data and systems from compromise. Here’s how you can do it:

- Isolate the affected systems immediately from the network.
- Change credentials and access details.
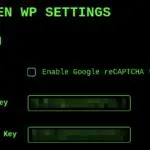
- Conduct a vulnerability scanning.
- Disable suspected vulnerable services from your website or internal network.
- Update and patch your systems.
Inform Affected Parties
Sometimes, informing affected parties, such as your existing customers, employees, partners, or even the general public, is a legal requirement and best practice. This step is evident in effectively managing the breach’s resultant and maintaining stakeholder trust. So you need to understand legal requirements, identify affected parity, and notify and provide necessary guidance to secure their information.
Figure out the Root Cause
It is an essential and critical step to determine what happened and caused the data breach. If you don’t know what happened, you can’t prevent the breach again. You need to investigate the incident carefully to address exploited vulnerabilities and the amount of data damaged. Here are the steps you can follow to find the root cause of the breach:
Forensic Team
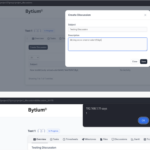
Assemble a team of highly qualified IT security experts. Including external cybersecurity experts who are specialized in digital forensics and can lead the investigation would be beneficial. Remember, sometimes, the internal experts might miss what an external expert can see. If you are rethinking that hiring an external expert can be expensive, contact Bytium.
Collect and Analyze Data
Gather all relevant data, such as server logs, traffic logs, access logs, and other records. These data are required for the IT team to determine the attacker’s steps and how the data breach occurred.
Addressing the Entry Point
Determine what kind of attack was successful for the initial access. Is it Phishing, Exploiting technical vulnerabilities, or through insider threats? Here, you must also interview staff to check for any suspected insider threats. Most of the time, cybercriminals get access either by exploiting employees or by exploiting technical vulnerabilities. Make sure to analyze from both sides.
Review Security Policy
Measure your existing security implementation and review the security policy to see if the attacker bypassed it. This will help you to identify any gaps in your network. Find out if your Antivirus, firewalls, and other security implementation is still effective. Remember, experienced hackers can bypass most antivirus programs by creating their own malware, firewalls, and IDs/IPS with more advanced payloads.
Remediation Plan
Develop a plan to remediate exploited vulnerabilities based on the IT Team’s investigation. Comprehensive vulnerability scanning or penetration testing can be included in the remediation plan. It is best to hire external experts to perform in-depth vulnerability scanning or penetration testing. From our experience, we have seen that we discovered many vulnerabilities, but the internal team missed them.
External team for penetration testing or to perform simple vulnerability scanning could be expensive solutions. But do you know we aim to make these services accessible for everyone(individuals to small to large size of businesses)? You can engage with us for a very low cost, but you will still get the highest quality result. Don’t hesitate to contact us if you are ever looking for someone to assess the security for an affordable cost.
Document Everything
Documenting everything about the entire data breach incident and the action taken is essential. It helps you learn from the incident and vital records for legal, regulatory, and recovery purposes. How can you do that? And what information should be documented? Here is an example of documentation of a data breach incident:

- Record how the data breach was discovered, including the alerts and different kinds of signs.
- Keep a detailed record of the investigation process, including vulnerabilities exploited, logs, affected systems, and communication-related to the data breach.
- Keep detailed reports of the initial to final decision taken and different types of evidence related to data breaches.
Conclusion
Dealing with a data breach can be tough, but handling it right is key. Quick action, a solid plan, and maybe some outside help can make a big difference. Remember, it’s not just about fixing things now – it’s also about learning and getting stronger for next time. Every breach is a chance to improve. Stay ready, stay sharp, and keep building up your defenses.
One of the best practices to prevent data breaches is conducting regular vulnerability scanning and performing comprehensive penetration testing to identify and remediate security weaknesses before malicious actors exploit them. Bytium offers very affordable security assessment services to strengthen your defense. Contact us to evaluate your systems!