Today, Bytium is launching its first product: Bytium Active.
 For years, Bytium has delivered hands-on security services — penetration tests, vulnerability programs, audit-readiness work — to teams that needed senior judgment on demand. That work taught us something uncomfortable: most small businesses don't have anyone watching between engagements. A pentest in March doesn't help when a certificate expires in July, a forgotten subdomain points to a deleted service in August, or a
For years, Bytium has delivered hands-on security services — penetration tests, vulnerability programs, audit-readiness work — to teams that needed senior judgment on demand. That work taught us something uncomfortable: most small businesses don't have anyone watching between engagements. A pentest in March doesn't help when a certificate expires in July, a forgotten subdomain points to a deleted service in August, or a .env file shows up in a public bundle in September.
Bytium Active is built to close that gap.
What Bytium Active Is
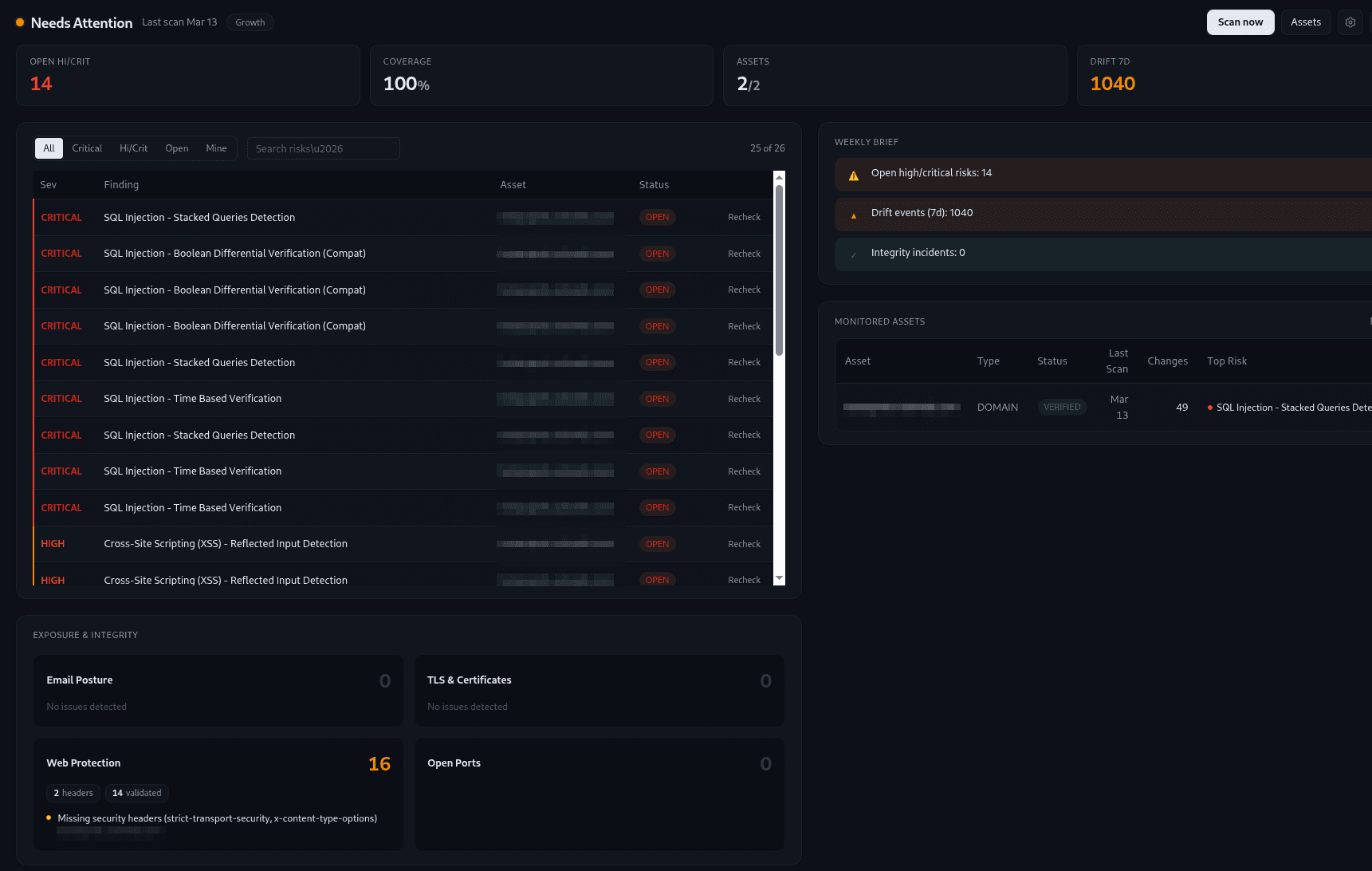
Bytium Active is a continuous monitoring product that watches the state of your business online. It's not a vulnerability scanner you point at code, and it's not another dashboard that flags a thousand things and asks you to triage them. It's a service that quietly runs in the background, surfaces what actually matters, and tells you — in plain language — what to do.
We organize what Active watches into four buyer concerns, only one of which is hackers:
- Don't get hacked. Exposed admin pages, leaked secrets, exposed
.env/.git/ backup files, open cloud buckets, weak configurations, and known vulnerabilities — surfaced with proof. - Don't go down. Expiring SSL certificates, expiring domains, and broken services flagged before they take your site offline or scare customers.
- Don't look unprofessional. Public dev environments, debug pages, broken configurations, and outdated technology versions — caught before customers see them.
- Be ready when asked. Exportable evidence and posture mapped to common frameworks. Ready for insurers, auditors, and enterprise customer questionnaires.
Each finding ships with proof and a clear next step. The point isn't to flag everything — it's to surface the right thing.
Why We Built It
Bytium services pay the bills, but they don't scale to the businesses that need security oversight the most: founders, side projects, agencies, and small businesses that can't afford a full security team or even a quarterly retainer.
Those businesses face the same risks larger ones do — leaked credentials, expired certificates, exposed environments, outdated software — but they get them in slow motion, and usually find out from a customer, an insurer, or a journalist.
Active was built to give those businesses the kind of continuous oversight that used to require either a full-time security hire or a five-figure annual contract. The same engine that backs Bytium's senior-led services now runs on a recurring schedule, packaged as a self-serve product, priced for teams that can't justify enterprise software.
Built by a Senior Operator
Bytium Active is built and run by Jobyer Ahmed — a senior security operator with OSCE³, CISSP, OSCP, and CNVP credentials, and years of running penetration tests and security programs. Under the hood is a recurring discovery and verification pipeline that orchestrates dozens of specialized engines, deduplicates noise, and ships proof with every finding. We translate that engine into plain answers, on a schedule you set, so you don't need a security team to know whether your business is healthy online.
Pricing That Makes Sense for Side Businesses
Active launches with three tiers, designed for individuals and small businesses:
- Starter — $19/month. Solo founders, freelancers, and side projects. One domain, weekly checks.
- Pro — $49/month. Small teams. Three domains, daily or weekly checks, full vulnerability coverage.
- Growth — $99/month. Small businesses scaling coverage. Ten domains, all scan cadences, premium enrichment.
Annual plans get roughly two months free. No long-term contracts, no procurement gymnastics, no quote-only enterprise tier.
What's Live Today
Active ships today with continuous discovery and verification of:
- Subdomain discovery and takeover risk detection
- TLS and certificate expiry tracking
- Web vulnerability detection
- Exposed admin panels, sensitive files, and cloud bucket misconfigurations
- Leaked secrets in public assets
- Outdated software fingerprinting
- Recurring scans on the cadence you choose
- Findings with reproducible proof and plain-language fix steps
- Posture mapped to common compliance frameworks
What's Coming Next
We're transparent about the roadmap because we want buyers to know what they're investing in. The next features in flight:
- Email security checks (SPF, DKIM, DMARC)
- Lookalike and typosquat domain detection
- Leaked credentials and breach exposure monitoring
- Domain and IP reputation / blocklist monitoring
- Dark web and paste site mentions of your brand
- Privacy basics (cookie banner, policy, GDPR essentials)
- Plain-language security score (A–F)
- Monthly PDF report with executive summary
- Email and SMS alerts on new findings
Each of these will land progressively over the coming months. Subscribers get them as they ship — no upgrade required.
Try It
Bytium Active is live now. You can sign up with Google or GitHub and get your first health check in minutes — no credit card required to register, no software to install, no agents to deploy.
Hire Bytium for senior-led services, or self-serve with Bytium Active. Same operator behind both.